Note: I shamelessly copied the whole post Steve Jenkins his blog, due to it being offline and requiring a safe place for this info…

As with all UBNT products, the EdgeMAX EdgeRouter products are not consumer-targeted devices. Ubiquiti makes business-classhardware only… so setting up most of their devices takes at least “pro-sumer†level ability. And with their EdgeRouter products, I recommend some network admin experience via the Linux command line (and at least a quick glance at their EdgeOS CLI Primer).
But if that’s you, and you’re sick of your browser warning you about an invalid certificate when you access your EdgeRouter admin interface, here’s the easy way to install your own custom SSL certificate on an EdgeRouter.
Step 1: Point a FQDN at your Router
Because an SSL certificate checks the validity of the hostname and/or domain name of the web server you’re accessing, you need to set up a FDQN (fully qualified domain name) to point at your EdgeRouter. Depending on how you access your router’s admin interface, and you could do this in a number of ways, and I’ll include a few examples below using hostname.example.com. Of course, you’ll need to use a hostname of your own choosing, as well as an actual domain name for which you have the ability to create certificates at a signing authority. You could just create a self-signed certificate in the EdgeMAX CLI (I’ve done it), but browsers like Chrome still won’t like that. Using a real certificate from a signing authority is what we’re looking to do here.
Example 1: If you only have internal access to your router’s admin GUI (which is the default), and you’re using your EdgeRouter as a local DNS resolver/forwarder (which is common), you can map a hostname to the internal IP of your router with the following command from the EdgeRouter’s CLI:
# set system static-host-mapping host-name hostname.example.com inet 192.168.1.1
You can test it from the EdgeOSÂ CLI with:
# /bin/ping hostname.example.com
UPDATE: As of EdgeOS 1.8, you can use the DNS host names feature wizard to handle this from the GUI. Put the full FQDN in the Host Name field, ignore the Alias field, put your router’s internal IP address in the IP Address field, then hit Apply.
Example 2: If you’ve got access to the zone file for your domain (or you’re using a hosted DNS service like CloudFlare), you can create an A record for the EdgeRouter’s internal IP address like this:
hostname.example.com. IN A 192.168.1.1
Example 3: If you only access the EdgeRouter from one or two systems on your internal network, you can add an entry to each system’s hosts file and point hostname.example.com to 192.168.1.1. Depending on your system (Windows, Mac, or Linux), your local hosts file location will vary. But I’m guessing that if you know enough to know that you want to use a real signed certificate with your EdgeRouter, you probably know where you local hosts file lives. 🙂
Example 4: This example assumes you’re willing to live with the security risks, and that you’ve opened up the firewall on your EdgeRouter to allow access to the admin interface from the WAN (if you want to do this, I recommend doing it on a non-standard port). It also assumes that you’re running your EdgeRouter on a dynamic IP address (like most home users would) and you’re using a DDNS service to point to your WAN IP (I’ve used Afraid.org since my DD-WRT router days). You won’t have authority to get a signed certificate for domain name owned by your DDNS provider. So instead, create a C record in the zone file for a domain you do control (like example.com), then point the C record at the FQDN of your DDNS hostname. If your DDNS hostname is ubnt.dyndns.org, create the following C record in the zone file of example.com:
hostname IN CNAME ubnt.dyndns.org.
There are obviously a number of ways to point a FQDN at either the internal (LAN) or external (WAN) IP address of your router, but whatever method you choose, just make sure that when you’re all done, an actual hostname and a domain name you control (or for which you have authority to generate signed certificates) resolves to an IP address that loads your router’s GUI.
Step 2: Generate a Key and Certificate Signing Request on the EdgeRouter
SSH to the CLI on your EdgeRouter, then get super-user privileges with:
$ sudo -i
I like to “cheat†at this part of the process and use DigiCert’s OpenSSL CSR Wizard to generate the OpenSSL command needed to generate the key and certificate signing request files. Start by filling out the Certificate Details:
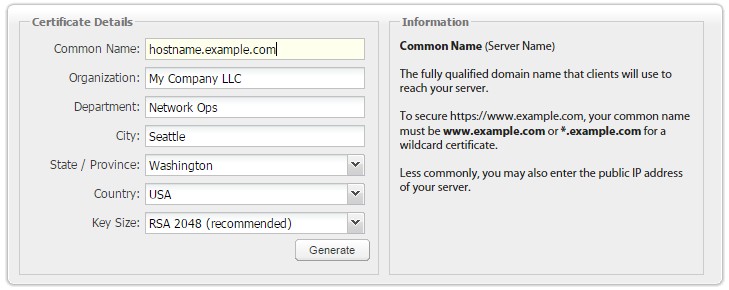
Using DigiCert’s OpenSSL CSR wizard
Once all the details are entered, hit the Generate button to create the OpenSSL command you’ll run from the EdgeRouter’s CLI command line:
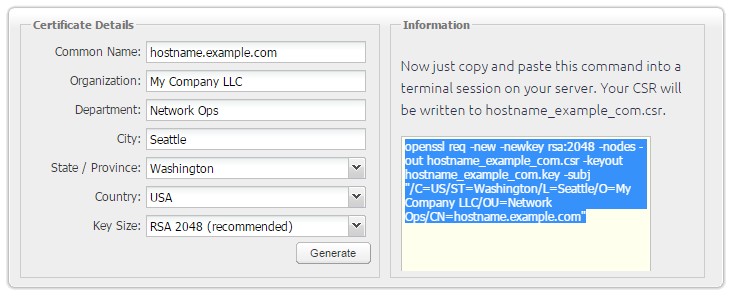
OpenSSL command ready to create a CSR
Copy the command and paste it into the EdgeRouter CLI as the super-user. Because SHA-1 certificates are set to expire after December 31, 2017, I recommend manually adding the -sha256 flag to the command to make sure your certificate is up-to-date.
# openssl req -sha256 -new -newkey rsa:2048 -nodes -out hostname_example_com.csr -keyout hostname_example_com.key -subj "/C=US/ST=Washington/L=Seattle/O=My Company LLC/OU=Network Ops/CN=hostname.example.com"
The output will look something like this:
Generating a 2048 bit RSA private key ......................................................+++ ................................................................+++ writing new private key to 'hostname_example_com.key' -----
Do an ls of the /root/ directory, and you should see two newly created files: hostname_example_com.key (your private key) and hostname_example_com.csr (your certificate signing request).
Step 3: Create the Certificate at your Signing Authority
Display the contents of your newly-created certificate signing request with:
# cat hostname_example_com.csr
Copy the contents of your CSR to your local clipboard, and be sure to include the first and last lines that say BEGIN CERTIFICATE REQUEST and END CERTIFICATE REQUEST.
Log in to the certificate authority of your choice. I like StartSSL, and I use one of their 100% free SSL certificates on my EdgeRouter (I’ve also written a post on how to get a free SSL cert from them for use with TLS in Postfix). Paste the contents of your CSR into your certificate authority’s interface. Once they’ve generated the signed certificate, you can either download the file it then upload it to the /root/ directory of your EdgeRouter, or do what I do: copy the certificate’s contents to the local clipboard, then use vi to create a hostname_example_com.crt file in the EdgeRouter’s CLI, paste the certificate’s contents in the new .crt file, then save and exit. Either way, we’ll assume you can figure out how to get the signed certificate into the /root/ directory (and we’ll assume it’s named hostname_example_com.crt).
Step 4: Merge the Contents of your Key and Certificate File into a .pem file
Back in the EdgeRouter CLI, combine the contents of your private key and the signed certificate into a file called server.pem with:
# cat hostname_example_com.key hostname_example_com.crt > server.pem
Step 5: Backup the Existing .pem file
Make a backup of the existing .pem file located in the EdgeRouter’s web server directory, so it’s easy to restore in case anything goes wrong:
# cp /etc/lighttpd/server.pem /root/server.pem.bak
Step 6: Copy the .pem file to the Web Server Directory
Overwrite the existing server.pem in the EdgeRouter’s web server directory with the new one you just created:
# cp /root/server.pem /etc/lighttpd/server.pem
Step 7: Reboot and Test
In order to start using your new certificate, the EdgeRouter’s web server needs to be restarted. You could reboot the entire router… but you’d lose Internet access for the few minutes it’s down (and anyone watching Netflix in the house while you do that will yell). Instead, since you’re already the super-user, stop the web server with:
# kill -SIGINT $(cat /var/run/lighttpd.pid)
then start it again with:
# /usr/sbin/lighttpd -f /etc/lighttpd/lighttpd.conf
FYI – these same commands will work with sudo if you ever need to restart the EdgeRouter web server while not the super-user.
Now go to your web browser and pull up the EdgeRouter’s admin interface from your browser using the FQDN you chose in Step 1 (if you use the IP address, you’ll still get the certificate error). You should no longer receive the warning from your browser, and the https: in your address bar won’t be red, or crossed out, or whatever your browser does to tell you it’s unhappy.
Congratulations! You just installed a valid SSL certificate for the admin interface in your EdgeMAX EdgeRouter!
Your questions, comments, and feedback are welcome below!